Where To Recycle Hard Drives in Los Angeles: 4 Drop Off Locations
It’s come time to dispose of your old PC or laptop, but you’re concerned about any remaining data that might remain on storage media. So where to recycle hard drives..
Protect Yourself With These 7 IT Asset Disposal Procedure
You’ve just ordered fresh IT office equipment, and to make room for the new gear you decide to put retired IT assets in the storeroom out back for a few..
How to Recycle Old Electronics
The high turnover of electronic equipment has many businesspeople wondering how to recycle old electronics in a secure and lawful way. Indeed, this is a question that is worth spending..
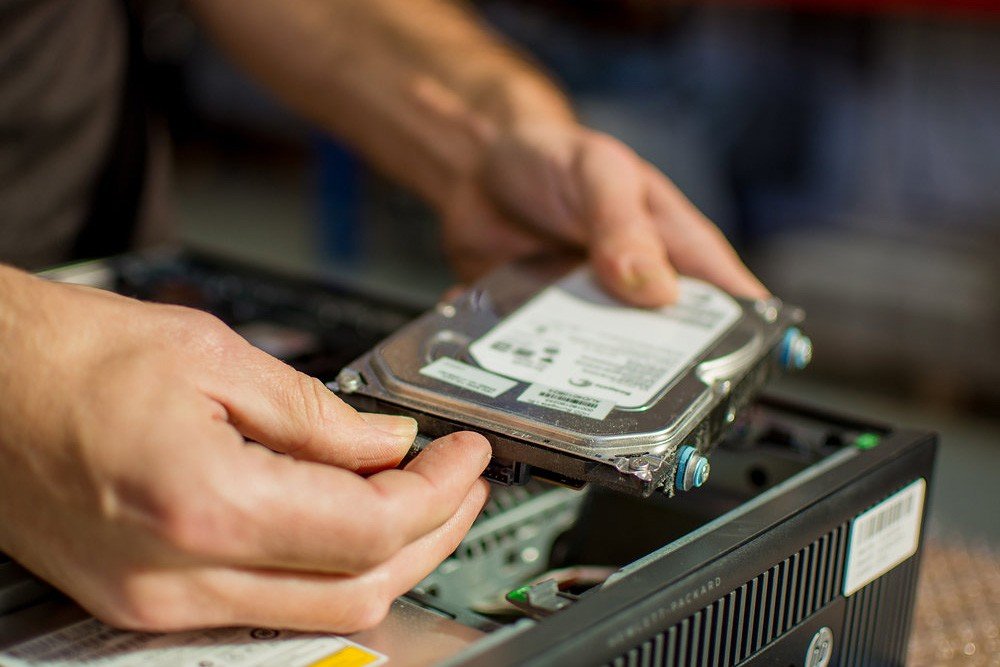
How to Recycle Hard Drives
Data breaches can affect companies and organizations of every size and across every industry. In 2011, Sony’s PlayStation network was hacked in what would become the worst data breach throughout..
What is the Purpose of Data Shredding?
Uber revolutionized the taxicab industry in 2009, but it wasn’t until late 2016 that it succumbed to one of the..
How to Destroy a Hard Drive
eBay is so well known that it almost rivals Coca-Cola as an internationally recognized brand name. That’s why the world..
What is the Disposal of An IT Asset?
September 2016 was a month to remember in the world of data destruction. It was the month that saw approximately 3 billion people have their personal information stolen in one..
What Is IT Asset Disposition (ITAD)?
IT Asset Disposition (ITAD) is a developing business need and a business service that all companies – no matter how large or small – may need to make use of..
Is Styrofoam Recyclable?
Foamed polystyrene – also known as Styrofoam – is a thermoplastic material used in countless everyday applications, but is Styrofoam recyclable? Foamed polystyrene is a lightweight plastic that’s essentially part..
How to Dispose of Old TV Parts like a DIY Hero
It’s easy for vintage enthusiasts to wax lyrical about the “vintage” chunky, boxy TVs of yesteryear – until they remember the picture quality. Despite daily use, no-one wanted the enormous..
How to Dispose of Electronics
Electronic devices have become an integral part of how we live, more so, our small, portable, and smart mobile phones that we carry everywhere we go. In fact, there were..
How to Dispose of Old Computers?
We use computers for everything: work, shopping, accounting, communication and even gaming. Rapid advances in computer technology guarantee that there will always be a better and faster device just around..
How to Destroy Hard Drive Data: and Hard Drives Themselves
Regardless of the kind of hard drive you use – magnetic hard drive disks or solid-state drives – knowing how to destroy a hard drive correctly is critical for the..
Recovering Valuable Resources and Minimizing Harm
Do you know how many old computers are discarded every year in the United States alone? Recent figures estimate that the figure is up to 20 million annually, and this..
PC Recycling 101: How to Dispose of Computer Components the Right Way
It used to be the case that motor vehicles were the worst culprit for rapidly becoming obsolete. But these days, that new car feeling seems to last a lifetime compared..
Where To Recycle Electronics, And Why It’s So Important
Did you know that, on average, each American household contains 24 electronic devices and gadgets? And with technology developing at an unprecedented rate and our lust for gadgets and electronics..
There’s A Right and A Wrong Way to Dispose of Old Computers
Computers, laptops, tablets, cell phones, e-readers: Americans can’t get enough of technology. Technology is developing at an almost unbelievable rate, and we are eager to jump on each new device..
More Than Risk Management With Secure IT Asset Disposition Services
An IT asset management plan dictates how IT assets are to be handled throughout their useful life and mandates the procedures that should be put in place to properly sanitize..
The Environmental And Economic Imperative For Recycling Computers
What a difference two decades can make! It was less than twenty years ago that computers were sometimes a luxury and sometimes a novelty. Schools often had one computer per..
Significance of Medical Data Breaches – Steps Healthcare Institutions
The Cost and Prevalence of Medical Data Breaches Research based on data from 2009 until 2016 suggests that the cost of medical data breaches has reached $363 per record, according..
How to Dispose of Batteries: The Only Guide You Need
Most people have a dead battery or two in their junk drawers and they probably don’t know how to dispose of batteries. Batteries are an important and reliable daily source..
Where To Dispose Of Electronics? Places You’ve Probably Never Heard Of
You should never just dispose of electronics in the trash. Electronic waste from computers and peripheral equipment such as CPUs, laptops, PDAs and networking systems contain potentially harmful components such..
The Top Recycling Programs In The U.S. for 2017
According to the US Environmental Protection Agency, Americans produce over 200 million tons of trash annually. Out of this, 75% is recyclable yet we only recycle, through recycling programs, about..
What Makes IT Asset Disposition Companies Safe and Secure
The past few years have transformed the IT landscape and organizations now are faced with the challenge of dealing with mounting e-waste. As a result, the services of IT asset..
Industry Best Practice to Destroy Your Data Securely
Over one-third of the organizations in the US lack active policies for the destruction of confidential data and information. And according to a study by the Ponemon Institute, more than..
Using Business Intelligence Software to Overcome Data Security Threats
Today’s business environment is faster than ever – and the use of effective business intelligence software to manage huge amounts of data gathered has never been as important as now...
What is ITAD and How Does it Work?
What is ITAD? IT Asset Disposition, or ITAD, is the process of recycling and disposing of an organization’s old electronic equipment and other IT resources using practices that are not..