What Is Data Destruction, The Best Ways To Erase Your Data Securely

It may be a term you’ve heard about, but not taken seriously before. So what is data destruction? What are the most effective methods to destroy data in storage media?
The end goal of any data destruction procedure is to make the information on a particular electronic device unreadable, but what is data destruction? And how comprehensive is the destruction process?
In this article, we look at the best data security measures that are used to secure your data and keep from prying eyes…

What Is Data Destruction?
The data destruction process utilizes various data destruction methods (e.g. degaussing, shredding and data wiping) to completely erase the data on all electronic devices including tapes, smartphones, tablets, hard drives, etc. so that it cannot fall into the wrong hands.
Why You Need Data Destruction
Proper data erasure is necessary because even the deleted files on your hard disk are not entirely wiped out. When you delete something on your device, the only thing that’s erased is the reference to the specific file – the actual file continues to exist. Even though the operating system is unable to find it, individuals who engage in data theft know how to restore deleted files.
Why is Securely Destroying Data Important?
Whether at home or in a business, dependence on electronic storage of data is universal. While electronics have greatly increased the convenience and efficiency of business operations, the incredible amount of digitized data poses a new risk for mismanagement and data breaches.
Incomplete or haphazard handling of a company’s data can range from inconvenient to catastrophic. Old hard drives that haven’t been accounted for may contain corporate financial records, personal employee information, or other privileged data that could be accessed in a data breach. If an outdated storage device contains any sensitive data, then it must be comprehensively destroyed or rendered untraceable.
Sensitive Data That Must Be Destroyed:
|
|
Avoiding a data breach should be among an organization’s top priorities. A breach of classified information can result in major financial and legal repercussions, and result in a loss of confidence in consumers.
On average, the cost of a data breach to a business is $3.86 million. Though those numbers may be skewed by large corporations, even a small business can take a major financial blow from lost records – IBM estimated that in 2018, the average cost per lost record is $148. Even inexpensive modern hard drives can store hundreds of thousands of records.
Securing all at-risk, outdated storage assets and destroying their data helps to guarantee security remains in the hands of an organization. But in the handling of these assets, there are legal guidelines on multiple levels to consider.
A company’s data destruction practices must comply with state and federal data security and privacy laws, and comply with various software licensing agreements. Compliance with such a legal framework is necessary to avoid consequences such as large fines.
Maintaining adherence to legal guidelines and calculating the appropriate approach to your company’s data destruction needs is an important process that requires diligence. A certified data sanitization service will provide the necessary methods for destruction while strictly following legal requirements.
How Does Secure Data Destruction Work?
Secure data destruction involves the complete obliteration of data, far beyond simply pressing the delete key or emptying the trash. Any device with sensitive company or customer information can be necessitated by internal guidelines, state regulations and federal statutes such as HIPAA to be comprehensively destroyed.
When data is destroyed, a company safeguards itself against potential data breaches and legal issues. By one or more of the processes described below, a hard drive previously loaded with privileged information can be rendered inaccessible.
The scale of a company’s operations and the breadth of the information stored will determine the proper method for data erasure. Some methods are more suitable for high-security operations, while others are more appropriate for devices in bulk.
In addition, different corporate and organizational requirements may determine the type of data destruction that a company can use.
What are the Different Types of Data Destruction?
In the past, data destruction simply meant throwing papers in the fire or utilizing a paper shredder. The nature of electronic data storage offers multiple different potential solutions, each of which has its benefits and drawbacks. Data destruction works by one of the following methods:

Data Wiping
Wiping data from hard drives is done typically by connecting them directly to a wiping device, or via a wiping software. Wiping retains the core function of the device for future use but can be a very time-intensive process.A complete wipe will often take multiple hours. Companies with large quantities of outdated hard drives might find the process to be hampered by time constraints. Smaller operations may benefit from wiping data because they can even provide a self-service data wipe with proper guidance. Data wipes can be very useful if an operation value maintaining their storage media for practical and financial reasons.
Overwriting
Software-based method of data erasure that completely overwrites all sectors of a hard disk drive or other digital storage media.
Data overwriting generally operates by the 2014 NIST 800-88 guidelines of erasure standards – requiring “a single overwrite pass with a fixed pattern such as binary zeros “ to destroy data permanently.
Overwriting is a widely used method in data destruction. Like wiping, overwriting is a time-intensive process and requires multiple hours for each device. Because this process requires access to information to mask it if a hard drive has been damaged or corrupted it cannot be overwritten.
Shredding/Crushing
Physical destruction of hard drive or other storage media by shredding or crushing components to a minute size, guaranteeing memory and function is irretrievable. The NIST states that destroying media is the safest and most bulletproof method for eliminating data.
Either one of these methods requires expensive physical capital like a shredder and a skilled operator but can be performed on-site as an added benefit. These methods are often employed when media wiping or degaussing processes are too inaccessible or incomplete.
Shredding/crushing are the most practical and economical options when performed on a bulk amount of storage media that would be too costly or complicated to degauss or wipe. Many hard drive shredding operations operate with favorable scale-based pricing for large operations.
In addition, physical destruction is undoubtedly the best assurance of complete inaccessibility. There is zero probability that a device could be repaired after the fact, and there is a peace of mind that comes with seeing the destroyed remains.
The most common forms of destroying a hard drive, tape or other magnetic media include:
|
|
Using any of these methods, there’s no way for anyone to retrieve any information stored on the device.
The main advantages of using this method over certified data wiping and degaussing are:
- It offers the highest level of security of all data deletion methods.
- It’s practically impossible to recover any of the destroyed data.
- It can destroy huge amounts of media at once.
- It has the ability to wipe out various kinds of media at the same time.
- It provides an ideal data wiping solution for businesses with large data centers.
Degaussing
Demagnetization of a hard drive tape or storage mechanism, neutralizing the device and obliterating the memory in the process. Media degaussing is one of the most secure forms of data destruction, because of the strong magnetism damages devices beyond usability. Degaussing is often employed by military personnel because it guarantees to disable the hard drive from being used again.
Degaussing electronic media means to decrease or completely wipe out the magnetic field (and the stored information) inside storage media like hard disks, cassettes, diskettes, tapes, and reels. The degausser demagnetizes the media using a potent magnetic field, which completely eliminates any data stored on the device.
So how does it work?
Every electronic device possesses a magnetic property named coercivity – the amount of magnetic field it takes to get the level of magnetization of a specific device to 0. Coercivity is measured in Oersteds (Oe) and depending on the Oe value of an electronic media, a degausser with either a higher or a lower magnetic field rating should be used to properly wipe out any stored info on the device.
Degaussing offers many advantages over standard data erasure (a.k.a. data wiping or overwriting) processes, including:
- It’s much safer – degaussing destroys every tiny bit of data.
- It takes very little time – a degaussing machine can wipe out data in under 10 seconds.
- It’s versatile – degaussing can eliminate information on any magnetic media.
- The degaussed electronic device can be later recycled.
Even though degaussing eliminates everything on hard drives (including startup files), which makes them completely unusable, most tapes can be used again, with the only exception of those that carry boot-up files or a servo-track.
What Data Security Laws do I Have to Worry About?
As data security has grown to be a more widespread concern, data security legislation has become more commonplace. As of this year, 25 states in the U.S. have enacted data security laws, most of which require businesses with sensitive data to implement “reasonable security procedures and practices” to prevent data breaches.
The specifics of each data security law vary from state to state – California abides by the Civilian Code 1798.81, which mandates that a “business shall take all reasonable steps to dispose of, or arrange for the disposal, of customer records”.
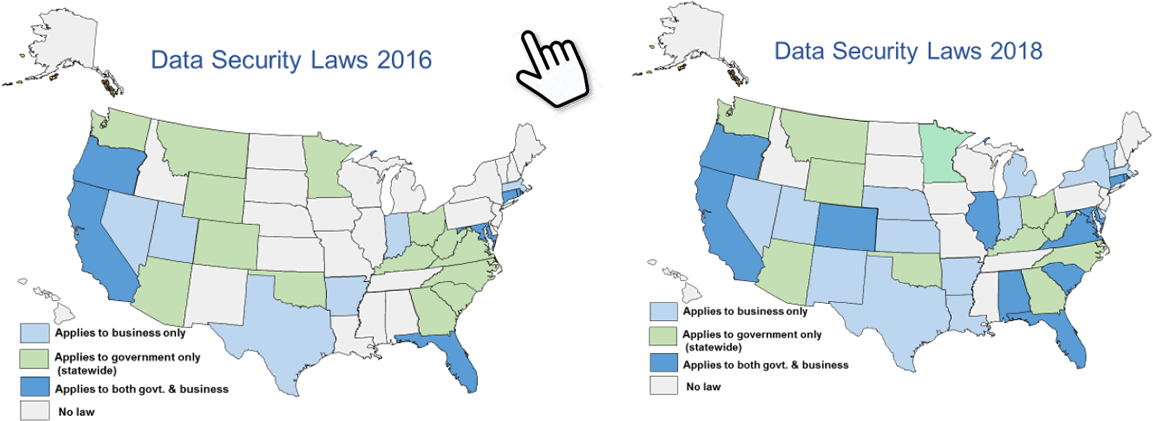
Federal information security legislation must also be taken into account when destroying old storage media. HIPAA was enacted by Congress in 1996 and remains the standard for data security regarding health insurance information. The Federal Trade Commission maintains the Disposal Rule which requires the comprehensive destruction of consumer report information.
Data disposal vendors that offer hard drive wiping and overwriting services are to be familiar with the National Institute of Science and Technology (NIST) 800.88 guidelines regarding the proper technique for effective data erasure. Guidelines and standards such as these aren’t required by law, but they provide a scientifically-backed framework that the best vendors comply with rigorously. An important benefit to a certified data disposal vendor service is that they are required to have comprehensive knowledge of industry best practices, and any applicable legislation to a given client. A respected data disposal vendor will prove their adherence to such regulations by documenting every step of the process and providing certification of destruction once the job is complete.
How do I Destroy my Company’s Data Securely?
Secure destruction of your company’s outdated storage media will first involve diligent documentation of all outdated hard drives and memory assets to guarantee everything is accounted for.
Counting any assets that have accumulated in areas of physical storage is vital. Drawers, closets, or other such locations can hide old drives and media that can end up in the wrong hands. Tally up a complete list of all devices that need to be destroyed and reference it continually to ensure accuracy.
Consolidating data and pertinent information that was once strewn across multiple sources can help your company to weed out even more outdated assets.
The next steps to securing destruction involve the services of a data destruction company. Entities that specialize in data sanitization are the highest option for guaranteed destruction.
A data destruction company will provide options depending on the nature and scale of a business’s disposal needs. Larger corporations with hundreds of assets will necessitate different methods than a small business with a couple of old drives laying around. Setting the logistical parameters for disposal with a vendor will set your company on the path to the destruction of old assets.
How Do I Find a Good Company that Offers Data Destruction Services?
Finding a good, reputable company to provide data destruction services can seem like a daunting task. The importance of data destruction as a comprehensive act leaves no margin for error. Two main indicators can help you decide if a company is worth its services.
- Reputation: Companies with tried and true reputations as data destruction specialists are the target option for any potential customer. A company that can point to its testimonials and history of industries served is the goal.
- Technical Knowledge: The various forms of data destruction can be complicated processes, and our constant evolution of methods and standards require industry professionals to be highly knowledgeable about the nuances of data destruction. Asking a company about its policies regarding new scientific guidelines will help you to determine the quality standards of a vendor.
- Convenience: Companies that offer on-site data destruction provide the added convenience of transportation, and adds a level of assurance with the physical presence of data destruction professionals.
Data destruction and erasure of all kinds is a highly critical process that can ensure the prevention of data breaches and allow a company to maintain compliance with state and federal data security laws.
AllGreen Recycling provides data destruction services for a range of storage media at all levels of scale and guarantees documentation of completion at every step of the process. Request a quote for your outdated assets, or click here to learn more about AllGreen’s data destruction capabilities.
Got a Truck Load of Hard Drives? Time To Use a Professional Media Shredding Service
What is data destruction? An integral part of any IT equipment’s life-cycle.
Our eco-friendly, secure data destruction services include off-site shredding options with specialized transport trucks that come to you. And we guarantee that your data is destroyed with a full chain of custody and a Certificate of Destruction.
Sources:
https://nvlpubs.nist.gov/nistpubs/specialpublications/nist.sp.800-88r1.pdf
