Data breaches are not exclusive to multinational corporations, even though most of the cybersecurity matters that make front page news relate to government departments or Fortune 500 companies. In anything, the consequences of a data breach on a small-medium bulk storage facility could be more disastrous than for a larger firm – relatively speaking – as the damages caused by lawsuits and compensation could potentially put a smaller company out of business
Data Security Issues for Small Bulk Storage Facilities
In many instances, larger companies have more resources to tide them through a data breach catastrophe, or may have even implemented costly cybersecurity insurance.
Small bulk storage facilities need to concern themselves with four main types of security:
|
|
When it comes to data security in particular, there are four actions that bulk storage facilities must undertake – both initially and then maintain on a regular basis – in order to keep their data secure.
- Identify and make an inventory of confidential data
- Put policies in place to protect the data
- Manage the risk of data breaches
- Note your particular vulnerabilities
With Technology Comes Increased Risk
Bulk storage facilities are thought to be one of the last industries to move into the technological world. It was only when bulk storage and self-storage operators realized the operational benefits of new technology that it started becoming integrated into the world of bulk storage.
However, with increased reliance on technology comes increased risk of liability, as technological solutions bring when them a corresponding risk of malfunction or data breach.
There’s Still a Place for Paper
As much as bulk storage facilities are increasingly relying on technology for their day-to-day operations, there is still a great reliance on paper in the industry. As such, companies need to ensure that they have procedures in place to destroy physical paperwork legally and responsibly.
Most people now recognize that simple recycling is not sufficient to destroy confidential paperwork. Similarly, even conventional shredding can be unsuitable for certain types of highly-sensitive documentation, however shredding services provided by data destruction companies ensure that all materials are completely destroyed and unable to be pieced back together.
Working with a world-class electronics recycling company is the only way of ensuring that your unwanted paperwork is destroyed, with no chance of risk for you.
Your Destruction Calendar
In addition, employ a method that advises you when your various categories of paperwork are due to be destroyed. Obsolete business plans, financial records old enough to no longer be required to be kept, and other paperwork older than a certain cut-off point should be regularly destroyed.
The IRS has a detailed list of how long business records should be kept, and the following chart from Organized Chaos Online also provides general guidance.
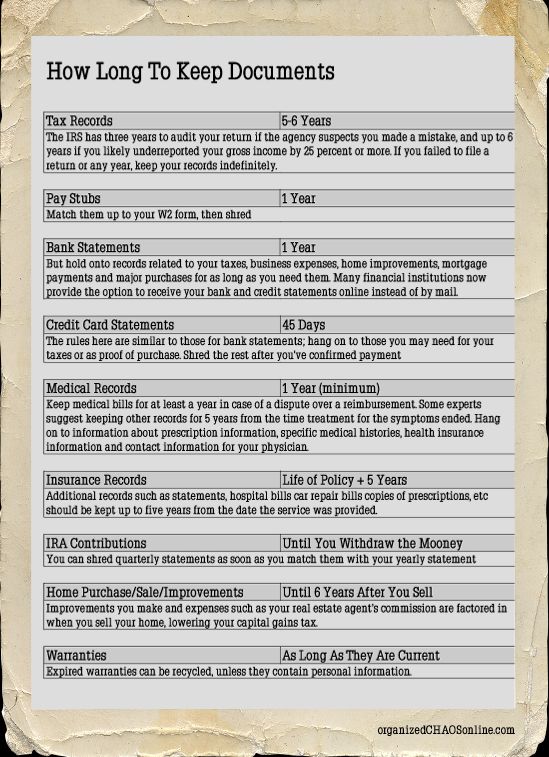
Image courtesy Organized Chaos Online
While it is important to keep all recent financial paperwork, employee records, and other pertinent paperwork, any paperwork that has passed its useful life should be destroyed. The less redundant paperwork you hold on to the better, and the easier it will be for you to maintain good records of your current paperwork. And, perhaps most importantly, the less chance there is of confidential paperwork going missing or being unaccounted for.
All Green Recycling offers regular pickups, assisting you to keep your stores of paperwork under control. Contact us today to discuss how ongoing data shredding can assist your business to manage its risk of data breaches.









